With so much of our lives taking place online, especially amid the Covid-19 pandemic, cybercriminals are getting increasingly inventive, using social engineering to persuade consumers to hand over information such as passwords and credit card details. Mass campaigns or individual attacks, phishing is both growing and evolving. That’s why we prepared a scary yet necessary list of phishing statistics to show you how sophisticated such schemes are anymore and hopefully, to give you an upper hand in your attempts to stay safe online — individually and professionally.
Phishing Statistics (Editor’s Choice)
- 82% of people use one password for multiple accounts. (Egress)
- Up to 98% of companies say they have security awareness programs in place. (Nira)
- 1.5 million new phishing websites are made monthly. (Swiss Cyber Institute)
- Stolen personal information costs $180 per record. (Egress)
- Up to 90% of cyberattacks are phishing attacks. (Spanning)
- It takes 250 days to discover a breach from compromised credentials. (Egress)
- Tech and pharma companies are the most vulnerable to phishing attacks. (Egress)
- The primary disguise of fraudulent emails is fake invoices. (Purplesac)
General Phishing Facts and Statistics
1. Email phishing accounts for 90% of ransomware attacks.
In those cases, the average ransom payment is around $200,000 and costs companies around three weeks in downtime. There are human costs too, with the victim fired or leaving voluntarily in 23% of the organizations that suffered such an attack.
(Egress, WP-Stack)
2. Up to 98% of companies have security awareness training.
While this is a very encouraging number, it has nothing to do with the effectiveness of such training. Statistics on phishing attacks training show that 64% of companies have formal programs with in-person training and computer-based practice and 30% use simulations of phishing attacks. Only 6% reported using different learning methods.
Around 74% of companies focused mainly on email phishing attacks training and only 44% included password creation, while 48% dealt with mobile device security.
(Nira)
3. 90% of threat actors rely on spear-phishing to infiltrate a company’s internal network.
Spear phishing, which targets a specific person or group, seems to be the weapon of choice of Advanced Persistent Threat (APT) groups, phishing trends indicate. Then, as many as 96% of threat actors use this method to gather intelligence.
(Purplesac)
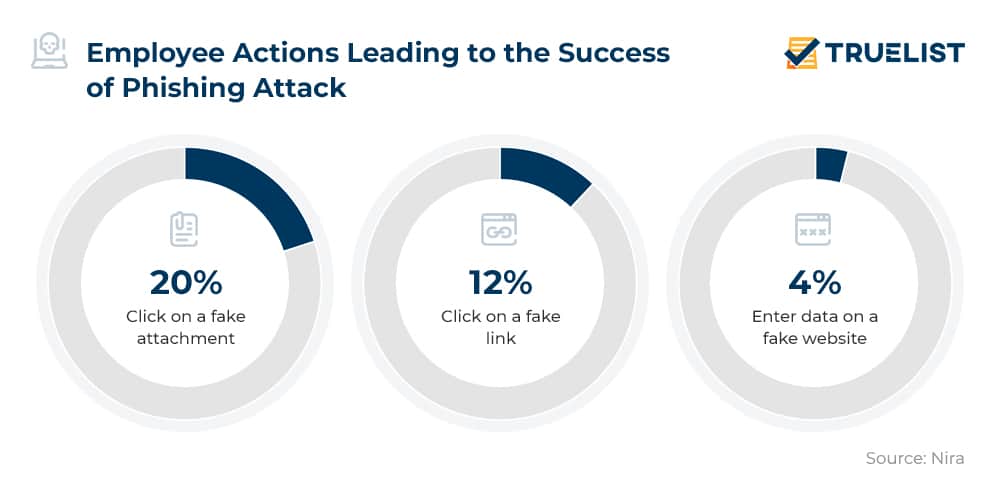
4. Workers will click on a fake attachment 20% of the time.
In case the email contains a link, around 12% of people will click on it. On the upside, only 4% will actually enter data into the website the link leads them to. Now, let’s see what makes employees click on fake links, according to email phishing statistics:
- A fake alert that someone attempted login from your social media account
- Verification of an incoming payment
- Possible suspension of a financial account due to missing personal data
- Software update
- Compromised health information
- Invitation to a Zoom meeting.
(Nira)
5. Around 1.5 million new phishing websites are created every month.
Phishing facts show that a lot of those websites impersonate well-known and trusted companies. Microsoft tops the list with 43%, followed by DHL with 18%, LinkedIn with 6%, and Amazon with 5%.
(Swiss Cyber Institute)
6. Phishing attacks that result in data breaches cost $4.65 million per attack.
Data breaches usually are not made of one attack but from a group of coordinated attack vectors. When the initial vector is phishing, costs can be massive. When phishing follows compromised email attacks, the cost of phishing attacks on average rises to $5.01 million per attack, phishing attack statistics show.
(Nira)
7. Phishing attacks saw a huge increase when the COVID pandemic started.
New to online and remote work both employers and employees were bound to make mistakes, and cyber criminals saw their chance. March 2020 saw 500,000 attacks alone, marking a massive spike in recent phishing attacks at the time, from 218,000 in January 2020. Covid itself proved quite the bait, with Google blocking 18 million malware and phishing emails about Covid in April 2020.
Global phishing statistics further show that out of all security incidents during 2020, 80% were phishing attacks.
(Nira)
8. Tech and healthcare companies are the most vulnerable to phishing attacks.
Stats point to the following industries where large companies are most affected by phishing:
- Technology with 60%
- Healthcare and Pharmaceuticals with 49%
- Manufacturing with 47%.
For medium-sized organizations:
- Construction with 50%
- Healthcare and Pharmaceuticals with 49%
- Business Services with 44%.
Among small companies the most endangered, according to phishing statistics, are:
- Healthcare and Pharmaceuticals with 45%
- Education with 42%
- Manufacturing with 41%.
(Egress)
9. Fake invoices are the number one disguise for the distribution of malware.
The most successful phishing emails are often disguised as:
- Bill or invoice – 7%
- Email delivery failure – 3%
- Package delivery – 4%
- Legal or law enforcement message – 1.1%
- Scanned document – 0.3%.
Most common phishing attacks are done through emails with attachments, these the kinds that carry the most risk are :
- Microsoft Word – 39.3%
- Microsoft Excel – 8.7%
- Executable – 19.5%
- Rich text – 14%
- Java archive files – 5.6%
This is where email encryption software with anti-phishing functionalities could come in handy, minimizing the chances of successful phishing attacks done through emails.
(Purplesec)
10. The average annual cost of phishing for US companies stands at $14.8 million.
Even one breach is quite costly and time-consuming as IBM’s Cost of a Data Breach phishing scam statistics show. The average cost of $3.86 million per breach in 2020 became 4.24 million in 2021. On the upside, those businesses that have used cybersecurity services, and AI in particular save up to $3.81 million.
(Egress)
11. LinkedIn has emerged as the top social media subject to watch out for.
With a massive 47%, phishing messages related to the professional network are the top social media subject to beware, according to social media phishing statistics. KnowBe4, which examined tens of thousands of email phishing lines from simulated tests, further notes that attacks related to working from home have logically been on the rise amid the Covid pandemic.
(KnowBe4)
12. Up to 85% of phishing attempts go after user credentials.
Around 20% of data breaches start by getting compromised user credentials. This is not hard, with 82% of people using the same passwords for multiple accounts. Once stolen, personally identifiable information is worth $180 per record, while the breach might take as long as 250 days to discover.
(Egress)
Phishing Statistics Worldwide
13. Around 63% of global employees can describe what phishing is.
It seems that under two-thirds of the global workforce knows accurately what phishing is. Stats further show that US employees underperform in that regard. Let’s have a look at how many employees can successfully describe what is phishing:
- 69% of UK workers
- 66% of Australian workers
- 66% of Japanese workers
- 64% of German workers
- 63% of French workers
- 63% of Spanish workers
- 52% of American workers.
(Nira)
14. One in three Canadians has encountered a phishing attack since the onset of the pandemic.
Phishing statistics for Canada show that scammers have included Covid into their repertoire, with emails often resembling Canada Recovery Benefit or the Canada Emergency Student Benefit payments, or offering Covid tests and vaccines for sale. Scammers have also been tricking people with emails about fake vaccine appointments or requests for money to support patients or research.
(Government of Canada)
15. The most phishing attacks in the Philippines happen in the national capital region.
Around 58,200 phishing attack victims were reported in 2019 in the region of the country’s national capital. The regions with the lowest phishing attack rate according to phishing statistics for the Philippines were Caraga and region 10 with 0.88% and 0.72% respectively.
(Statista)
16. Australia had over 44,000 phishing incidents in 2020.
Just like the case with Canada, Australia also saw a massive spike in phishing attacks amid the coronavirus pandemic, with scammers taking advantage of panic and lockdowns and costing Australians a massive A$176,1 million (~$122 million). The country saw an increase of 75% in phishing incidents in 2020 from the 25,168 incidents reported Down Under just a year ago, according to phishing statistics for Australia.
(Channel Life)
17. Up to 83% of companies in India saw a rise in phishing during the pandemic.
Pandemic-induced phishing did not pass by India either. Heightened targeting of IT teams in the country as the pandemic hit was reported by the vast majority of tech companies. On the upside, as many as 98% of organizations in the country report having implemented a program or programs to counter phishing attacks. 67% use a computer-based training program, 60% rely on a human-led program, and 51% use phishing simulations, according to phishing statistics for India.
(Live Mint)
18. The UK has a 20% higher phishing attempt rate than the global average.
On average, one in every 3,722 emails sent in the UK represents a phishing attempt. The result is that 43% of organizations across the nation have identified cyber breaches or attacks in 2020 alone. Even more alarming is that every 19 seconds, a small business in the UK is being hacked, according to phishing statistics for the UK. SMEs meanwhile 65,000 daily hacking attempts, 4,500 of which, unfortunately, turn out to be successful.
(Data Basix)
In Conclusion
The key to avoiding falling victim to phishing and its many forms is to educate yourself and your employees (in case you are a business owner) and stay vigilant at all times. While most companies around the world claim to have proper cybersecurity programs in place to train staff, when it comes to results, phishing statistics suggest that their effectiveness still has a long way to go.
FAQs
What percentage of cyberattacks are phishing?
Up to 90% of cyber-attacks are phishing attacks according to CISCO’s 2021 Cybersecurity Threat Trends report. Out of those, 65% is spear phishing, which is the most common type of attack.
(Spanning)
How many phishing emails are sent daily?
A 3.4 billion phishing emails are sent daily, and the annual number goes way beyond one trillion. The figure is growing and the threats are getting more sophisticated.
(Valimail)
How many businesses are targeted by spear-phishing attacks each day?
Spear phishing statistics show that It is nearly impossible to get an accurate estimate of how many businesses are targeted by spear phishing in a day, but we can look at the fact that 88% of companies are attacked every year, which means anyone is open for an attack every day.
(Norton)
What percentage of people fall for phishing?
Up to 61% of people would not recognize a fraudulent website and are at constant risk of falling for phishing. When asked if they were a victim of a phishing attack 24% said yes, and 22% did not know.
(PR Newswire)
What is the success rate of phishing attacks?
In 86% of organizations, at least one person opened a phishing link according to CISCO’s 2021 Cybersecurity threat trends report.
(Tessian)
Which country has the highest email phishing rate?
Phishing attacks statistics show that the highest phishing rate can be found in Mongolia with 15.54%, followed by Israel with 15.24%, France with 12.58%, Brasil with 11.86%, and Cameroon with 10.87%.
(Statista)
Where do most phishing emails come from?
Most of the latest phishing emails come from Eastern Europe. The main sources are considered to be Lithuania, Latvia, Serbia, Ukraine, and Russia.
(Info Security)
What is the most common type of phishing?
The most common phishing types are deceptive phishing, spear phishing, whaling, vishing, smishing, and pharming.
(Tripwire)
What is whaling in phishing?
Whaling is a specific type of phishing that targets executives and senior management, it is usually an email with the goal of inducing a money transfer. Phishing stats show it usually happens by impersonating a company that frequently receives payments from the victims already and the emails look very familiar. Payment is done by default without noticing and the fraud is enabled by the employee’s low attention.
(NCSC)
What is the difference between phishing and spam?
Spam is an unwanted, uninvited, unsolicited email or an instant message including those on social media messages spam statistics show. Phishing is a malicious attempt, an email sent from cybercriminals meant to extract sensitive or confidential information from someone mistaking the sender for legitimate sources such as a well-known company, business partner, someone higher up in the company, and similar. Phishing statistics show that this could result in identity theft or financial losses while spam usually consists of advertising and simply wastes your time.
(Egress, Texas Tech University)
Sources: Egress, WP-Stack, Nira, Swiss Cyber Institute, Spanning, Purplesac, KnowBe4, Government of Canada, Statista, Channel Life, Live Mint, Data Basix, Valimail, Norton, PR Newswire, Tessian, Statista, Info Security, Tripwire, NCSC, Texas Tech University

